- How to run sudo command without a password on a Linux or Unix
- How to to run sudo command without a password:
- How do I execute ALL sudo commands without password?
- How do I test it?
- Conclusion
- Using sudo on linux
- Contents
- Installation
- Usage
- Configuration
- Defaults skeleton
- View current settings
- Using visudo
- Example entries
- Sudoers default file permissions
- Tips and tricks
- Disable password prompt timeout
- Add terminal bell to the password prompt
- Passing aliases
- Disable per-terminal sudo
- Reduce the number of times you have to type a password
- Environment variables
- Root password
- Disable root login
- kdesu
- Harden with sudo example
- Configure sudo using drop-in files in /etc/sudoers.d
- Editing files
- Enable insults
- Troubleshooting
- SSH problem without TTY
- Permissive umask
How to run sudo command without a password on a Linux or Unix
I ‘m a new Unix system user. How do I use sudo command without a password on a Linux or Unix-like systems? I log in as tom@my-cloud-server-ip and disabled root login for ssh. After login, I need to run some commands as root user. I am the only sysadmin using my server. How do I run or execute sudo command without a password for a user named Tom under Debian/Ubuntu/CentOS Linux cloud server?
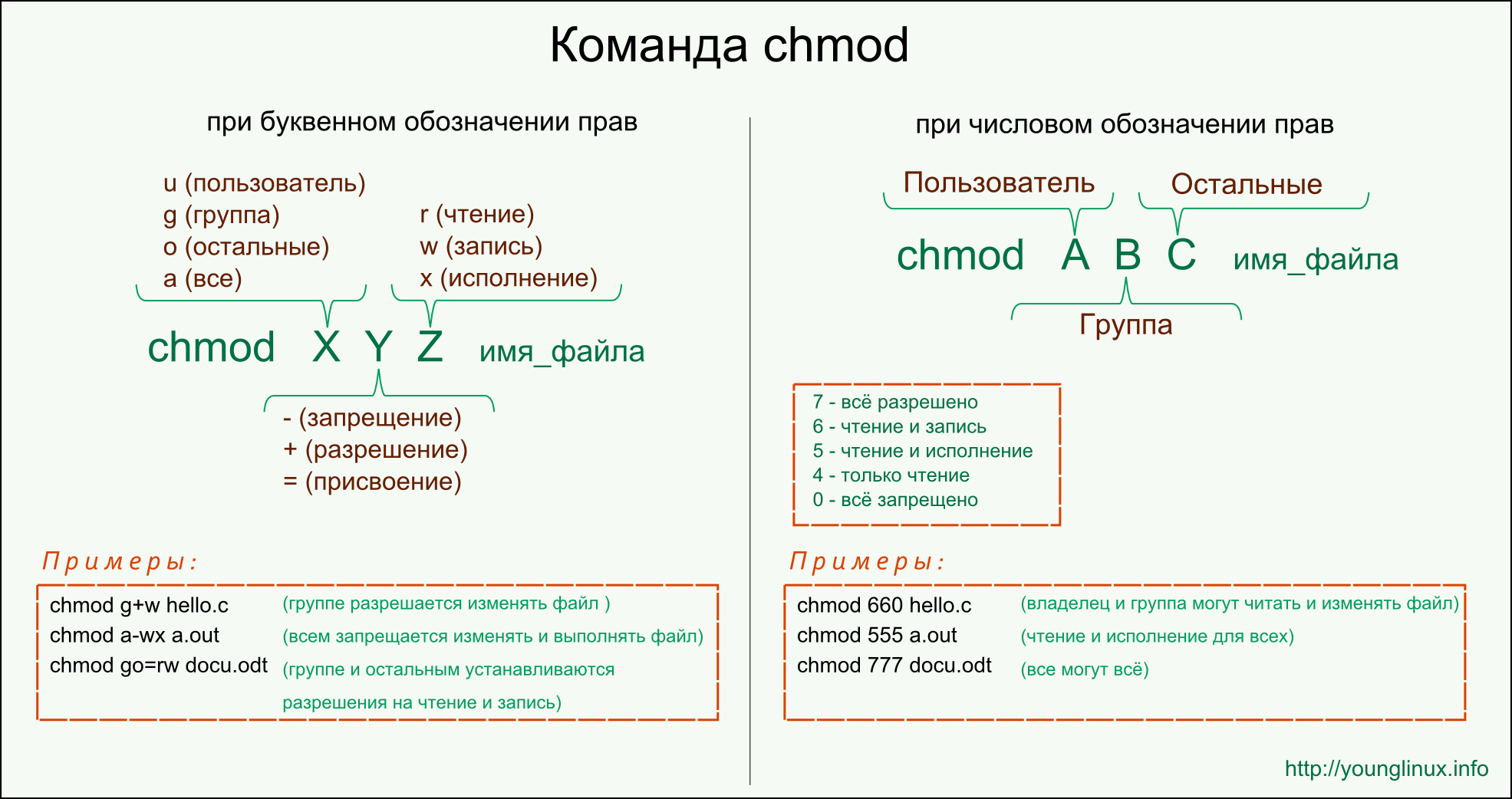
sudo (“superuser do”) is nothing but a tool for Linux or Unix-like systems to run commands/programs as another user. Typically as a root user or another user. You can delegate common tasks such as reboot the server or restart the Apache or make a backup using sudo for unprivileged users. By default, sudo needs that a user authenticates using a password before running a command. Some times you may need to run a command with root privileges, but you do not want to type a password using sudo command. This is useful for scripting or any other purpose. This can be achieved by editing /etc/sudoers file and setting up correct entries. You need to consider any security consequence of allowing a sudo command execute without a password.
| Tutorial details | |
|---|---|
| Difficulty level | Easy |
| Root privileges | Yes |
| Requirements | sudo on Linux or Unix/BSD/macOS |
| Est. reading time | 3 mintues |
NOTE: Initial setup must be done using the root account. One can gain root access by directly log in as root using console, ssh, or su command:
su —
In all cases, you must know the root password in advance before sudo can be configured to commands without a password. You might have sudo access and grant another user account passwordless access for commands.
How to to run sudo command without a password:
- Gain root access: su —
- Backup your /etc/sudoers file by typing the following command:
cp /etc/sudoers /root/sudoers.bak - Edit the /etc/sudoers file by typing the visudo command:
visudo - Append/edit the line as follows in the /etc/sudoers file for user named ‘vivek’ to run ‘/bin/kill’ and ‘systemctl’ commands:
vivek ALL = NOPASSWD: /bin/systemctl restart httpd.service, /bin/kill - Save and exit the file.
How do I execute ALL sudo commands without password?
Type the following command as root user:
# visudo
Or if you have sudo access and want to grant another user permission, try:
$ sudo visudo
Append the following entry to run ALL command without a password for a user named tom:
- No ads and tracking
- In-depth guides for developers and sysadmins at Opensourceflare✨
- Join my Patreon to support independent content creators and start reading latest guides:
- How to set up Redis sentinel cluster on Ubuntu or Debian Linux
- How To Set Up SSH Keys With YubiKey as two-factor authentication (U2F/FIDO2)
- How to set up Mariadb Galera cluster on Ubuntu or Debian Linux
- A podman tutorial for beginners – part I (run Linux containers without Docker and in daemonless mode)
- How to protect Linux against rogue USB devices using USBGuard
Join Patreon ➔
Here is my sample config file:
Fig.01: How to execute sudo without password for tom user
How do I test it?
Simply run /bin/kill to kill any process without a password:
[vivek@server ]$ sudo /bin/kill pid-here
OR
[vivek@server ]$ sudo /bin/systemctl restart httpd.service
Conclusion
You learned how to run a command without a password when using sudo on Linux or Unix-like systems. There is a significant security risk associated with passwordless operations. Hence, I would strongly recommend NOT doing this, but as they say, “it is not UNIX’s job to stop you from shooting your foot. If you so choose to do so, then UNIX’s job is to deliver Mr. Bullet to Mr. Foot in the most efficient way it knows.” For more info read man pages:
visudo(8)
🐧 Get the latest tutorials on Linux, Open Source & DevOps via
Источник
Using sudo on linux
Sudo allows a system administrator to delegate authority to give certain users—or groups of users—the ability to run commands as root or another user while providing an audit trail of the commands and their arguments.
Sudo is an alternative to su for running commands as root. Unlike su, which launches a root shell that allows all further commands root access, sudo instead grants temporary privilege elevation to a single command. By enabling root privileges only when needed, sudo usage reduces the likelihood that a typo or a bug in an invoked command will ruin the system.
Sudo can also be used to run commands as other users; additionally, sudo logs all commands and failed access attempts for security auditing.
Contents
Installation
Usage
To begin using sudo as a non-privileged user, it must be properly configured. See #Configuration.
To use sudo, simply prefix a command and its arguments with sudo and a space:
For example, to use pacman:
See sudo(8) for more information.
Configuration

Defaults skeleton
sudoers(5) § SUDOERS OPTIONS lists all the options that can be used with the Defaults command in the /etc/sudoers file.
See [1] for a list of options (parsed from the version 1.8.7 source code) in a format optimized for sudoers .
See sudoers(5) for more information, such as configuring the password timeout.
View current settings
Run sudo -ll to print out the current sudo configuration, or sudo -lU user for a specific user.
Using visudo
The configuration file for sudo is /etc/sudoers . It should always be edited with the visudo(8) command. visudo locks the sudoers file, saves edits to a temporary file, and checks it for syntax errors before copying it to /etc/sudoers .
The default editor for visudo is vi. The sudo package is compiled with —with-env-editor and honors the use of the SUDO_EDITOR , VISUAL and EDITOR variables. EDITOR is not used when VISUAL is set.
To establish nano as the visudo editor for the duration of the current shell session, export EDITOR=nano ; to use a different editor just once simply set the variable before calling visudo:
Alternatively you may edit a copy of the /etc/sudoers file and check it using visudo -c /copy/of/sudoers . This might come in handy in case you want to circumvent locking the file with visudo.
To change the editor permanently, see Environment variables#Per user. To change the editor of choice permanently system-wide only for visudo, add the following to /etc/sudoers (assuming nano is your preferred editor):
Example entries
To allow a user to gain full root privileges when they precede a command with sudo , add the following line:
To allow a user to run all commands as any user but only on the machine with hostname HOST_NAME :
To allow members of group wheel sudo access:
To disable asking for a password for user USER_NAME :
Enable explicitly defined commands only for user USER_NAME on host HOST_NAME :
Enable explicitly defined commands only for user USER_NAME on host HOST_NAME without password:
A detailed sudoers example is available at /usr/share/doc/sudo/examples/sudoers . Otherwise, see the sudoers(5) for detailed information.
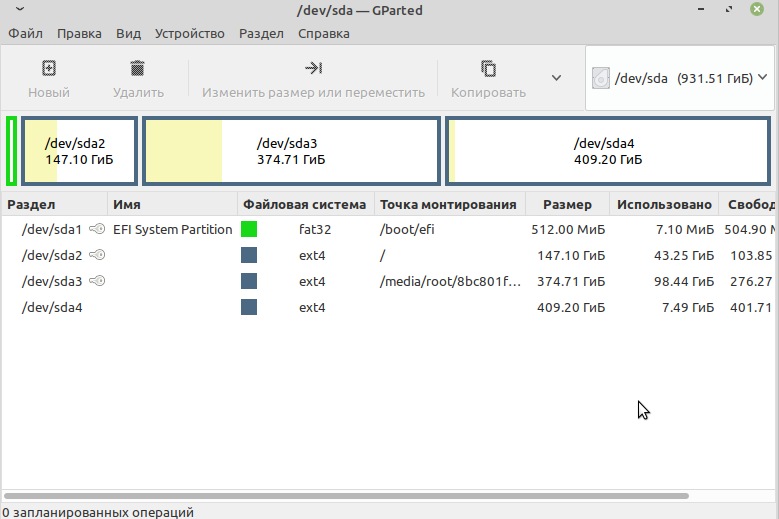
Sudoers default file permissions
The owner and group for the sudoers file must both be 0. The file permissions must be set to 0440. These permissions are set by default, but if you accidentally change them, they should be changed back immediately or sudo will fail.
Tips and tricks
Disable password prompt timeout
A common annoyance is a long-running process that runs on a background terminal somewhere that runs with normal permissions and elevates only when needed. This leads to a sudo password prompt which goes unnoticed and times out, at which point the process dies and the work done is lost or, at best, cached. Common advice is to enable passwordless sudo, or extend the timeout of sudo remembering a password. Both of these have negative security implications. The prompt timeout can also be disabled and since that does not serve any reasonable security purpose it should be the solution here:
Add terminal bell to the password prompt
To draw attention to a sudo prompt in a background terminal, users can simply make it echo a bell character:
Note the ^G is a literal bell character. E.g. in vim, insert using the sequence Ctrl+v Ctrl+g , or in nano, Alt+v Ctrl+g .
Passing aliases
If you use a lot of aliases, you might have noticed that they do not carry over to the root account when using sudo. However, there is an easy way to make them work. Simply add the following to your
/.bashrc or /etc/bash.bashrc :
Disable per-terminal sudo
If you are annoyed by sudo’s defaults that require you to enter your password every time you open a new terminal, set timestamp_type to global :
Reduce the number of times you have to type a password
If you are annoyed that you have to re-enter your password every 5 minutes (default), you can change this by setting a longer value for timestamp_timeout (in minutes):
If you are using a lot of sudo commands on a row, it is more logical to refresh the timeout every time you use sudo than to increase timestamp_timeout . Refreshing the timeout can be done with sudo -v (whereas sudo -K revokes immediately).
You might want to automate this by adding the following to your .bashrc :
It is also possible to use a bash function; for more details see stackexchange.
Environment variables
If you have a lot of environment variables, or you export your proxy settings via export http_proxy=». » , when using sudo these variables do not get passed to the root account unless you run sudo with the -E option.
The recommended way of preserving environment variables is to append them to env_keep :
Root password
Users can configure sudo to ask for the root password instead of the user password by adding targetpw (target user, defaults to root) or rootpw to the Defaults line in /etc/sudoers :
To prevent exposing your root password to users, you can restrict this to a specific group:
Disable root login
Users may wish to disable the root login. Without root, attackers must first guess a user name configured as a sudoer as well as the user password. See for example OpenSSH#Deny.
The account can be locked via passwd :
A similar command unlocks root.
Alternatively, edit /etc/shadow and replace the root’s encrypted password with «!»:
To enable root login again:
kdesu
kdesu may be used under KDE to launch GUI applications with root privileges. It is possible that by default kdesu will try to use su even if the root account is disabled. Fortunately one can tell kdesu to use sudo instead of su. Create/edit the file
or use the following command:
Alternatively, install kdesudo AUR , which has the added advantage of tab-completion for the command following.
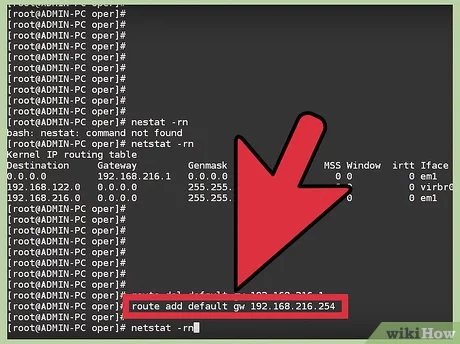
Harden with sudo example
Let us say you create 3 users: admin, devel, and joe. The user «admin» is used for journalctl, systemctl, mount, kill, and iptables; «devel» is used for installing packages, and editing config files; and «joe» is the user you log in with. To let «joe» reboot, shutdown, and use netctl we would do the following:
Edit /etc/pam.d/su and /etc/pam.d/su-l Require user be in the wheel group, but do not put anyone in it.
Limit SSH login to the ‘ssh’ group. Only «joe» will be part of this group.
Add users to other groups.
Set permissions on configs so devel can edit them.
With this setup, you will almost never need to login as the Root user.
«joe» can connect to his home WiFi.
«joe» can not use netctl as any other user.
When «joe» needs to use journalctl or kill run away process he can switch to that user.
But «joe» cannot switch to the root user.
If «joe» want to start a gnu-screen session as admin he can do it like this:
Configure sudo using drop-in files in /etc/sudoers.d
sudo parses files contained in the directory /etc/sudoers.d/ . This means that instead of editing /etc/sudoers , you can change settings in standalone files and drop them in that directory. This has two advantages:
- There is no need to edit a sudoers.pacnew file;
- If there is a problem with a new entry, you can remove the offending file instead of editing /etc/sudoers (but see the warning below).
The format for entries in these drop-in files is the same as for /etc/sudoers itself. To edit them directly, use visudo -f /etc/sudoers.d/somefile . See sudoers(5) § Including other files from within sudoers for details.
The files in /etc/sudoers.d/ directory are parsed in lexicographical order, file names containing . or
are skipped. To avoid sorting problems, the file names should begin with two digits, e.g. 01_foo .
Editing files
sudo -e or sudoedit lets you edit a file as another user while still running the text editor as your user.
This is especially useful for editing files as root without elevating the privilege of your text editor, for more details read sudo(8) § e .
Note that you can set the editor to any program, so for example one can use meld to manage pacnew files:
Enable insults
Users can enable insults easter egg in sudo by adding the following line in sudoers file with visudo .
Upon entering an incorrect password this will replace Sorry, try again. message with humorous insults.
Troubleshooting
SSH problem without TTY

SSH does not allocate a tty by default when running a remote command. Without a allocated tty, sudo cannot prevent the password from being displayed. You can use ssh’s -t option to force it to allocate a tty.
The Defaults option requiretty only allows the user to run sudo if they have a tty.
Permissive umask

Sudo will union the user’s umask value with its own umask (which defaults to 0022). This prevents sudo from creating files with more open permissions than the user’s umask allows. While this is a sane default if no custom umask is in use, this can lead to situations where a utility run by sudo may create files with different permissions than if run by root directly. If errors arise from this, sudo provides a means to fix the umask, even if the desired umask is more permissive than the umask that the user has specified. Adding this (using visudo ) will override sudo’s default behavior:
This sets sudo’s umask to root’s default umask (0022) and overrides the default behavior, always using the indicated umask regardless of what umask the user as set.
Источник