- Arch linux vnc server
- Contents
- Installation
- Configuration
- Running on a headless server
- TigerVNC
- Contents
- Installation
- Running vncserver for virtual (headless) sessions
- Initial setup
- Starting and stopping tigervnc
- Expose the local display directly
- Running x0vncserver to directly control the local display
- Starting x0vncserver via xprofile
- Starting and stopping x0vncserver via systemd
- Running Xvnc with XDMCP for on demand sessions
- Connecting to vncserver
- Passwordless authentication
- Example GUI-based clients
- Accessing vncserver via SSH tunnels
- On the server
- On the client
- Connecting to a vncserver from Android devices over SSH
- Tips and tricks
- Connecting to an OSX system
- Recommended security settings
- Toggling fullscreen
- Workaround for mouse back and forward buttons not working
- Substituting mouse back/forward buttons with keyboard keys XF86Back/XF86Forward
- Mapping the keyboard key presses back to mouse button clicks on the server
- Troubleshooting
- Terminals in vncserver start in / (root dir)
- Unable to type ‘
- Black rectangle instead of window
- Empty black window with mouse cursor
- No mouse cursor
- Copying clipboard content from the remote machine
- «Authentication is required to create a color managed device» dialog when launching GNOME 3
- No window decoration / borders / titlebars / cannot move windows around
- systemd service unit run as user
- Arch Linux User Repository
- Search Criteria
- Package Details: realvnc-vnc-server 6.7.4-1
- Package Actions
- Dependencies (4)
- Required by (0)
- Sources (6)
- Latest Comments
- BenTheTechGuy commented on 2021-05-04 21:01
- azasouth commented on 2021-04-21 10:15
- Kewl commented on 2021-04-21 07:10
- azasouth commented on 2021-04-21 01:40
- Kewl commented on 2021-04-15 20:22
- MattScherbatsky commented on 2021-04-15 19:17
- BenTheTechGuy commented on 2021-02-18 22:08
- void09 commented on 2021-01-06 22:26
- Kewl commented on 2019-09-28 07:56
- anch2150 commented on 2019-09-28 00:57
Arch linux vnc server

Vino is a VNC (Virtual Network Computing) server allowing remote connection to your actual desktop. It is a default component of the GNOME desktop environment.
Contents
Installation
You need to restart GNOME so that vino-server is started automatically when enabling the remote desktop feature. The remote desktop feature can usually be enabled in Settings > Sharing, however this only seems to be functional when NetworkManager is installed and functional.
Configuration
You can configure vino via gnome-control-center.
Now you can connect remotely to your desktop via a VNC viewer like TightVNC or Remmina. Remember to forward port 5900 if you are behind a NAT device and to allow the connection through iptables.
If you are having problems regarding security and encryption you could try:
If you use a standalone window manager like Openbox and it does not work, you can start vino-server manually or add the command to the window manager’s autostart script
Running on a headless server
Vino can be used to manage a headless server with a graphical desktop via VNC. For this, a graphics driver like xf86-video-dummy must be installed and configured. xpra’s sample xorg.conf for the Xdummy driver can be used as a base. Then, the server can be configured to start X at boot for the user account that should be usable remotely. Vino must be made to autostart with the desktop environment by creating a desktop entry in the user’s home directory such as this one:
Next, make Vino accept VNC connections without asking for confirmation by running the following command as the graphical desktop user:
You may wish to revoke suspend and hibernate permissions using Polkit.
For the GNOME desktop environment, the following are some further options you may want for GNOME:
Remember to configure your firewall to not block the rfb port used for VNC. For secure authentication – which should be used when giving access to privileged users on the open internet –, you should tunnel the VNC protocol through e.g. SSH or stunnel instead of unblocking the rfb port. When using stunnel, you should require a password:
You can now log in to your server with a VNC client such as vinagre .
Источник
TigerVNC
TigerVNC is an implementation of the Virtual Network Computing (VNC) protocol. This article focuses on the server functionality.
Contents
Installation
Running vncserver for virtual (headless) sessions
Initial setup
For a quick start, see the steps below. Users are encouraged to read vncserver(8) for the complete list of configuration options.
- Create a password using vncpasswd which will store the hashed password in
/.vnc/passwd .
/.vnc/config and at a minimum, define the type of session desired with a line like session=foo where foo corresponds to whichever desktop environment is to run. One can see which desktop environments are available on the system by seeing their corresponding .desktop files within /usr/share/xsessions/ . For example:
Starting and stopping tigervnc
Start an instance of the vncserver@.service template and optionally enable it to run at boot time/shutdown. Note that the instance identifier in this case is the display number (e.g. instance vncserver@:1.service for display number :1 ).
Expose the local display directly
Tigervnc comes with libvnc.so which can be directly loaded during X initialization which provides better performance. Create a following file and restart X:
Running x0vncserver to directly control the local display
tigervnc also provides x0vncserver(1) which allows direct control over a physical X session. After defining a session password using the vncpasswd tool, invoke the server like so:
Starting x0vncserver via xprofile
A simple way to start x0vncserver is adding a line in one of the xprofile files such as:
Starting and stopping x0vncserver via systemd
In order to have a VNC Server running x0vncserver, which is the easiest way for most users to quickly have remote access to the current desktop, create a systemd unit as follows replacing the user and the options with the desired ones:
Running Xvnc with XDMCP for on demand sessions
One can use systemd socket activation in combination with XDMCP to automatically spawn VNC servers for each user who attempts to login, so there is no need to set up one server/port per user. This setup uses the display manager to authenticate users and login, so there is no need for VNC passwords. The downside is that users cannot leave a session running on the server and reconnect to it later.
To get this running, first set up XDMCP and make sure the display manager is running. Then create:
Use systemctl to start and enable xvnc.socket . Now any number of users can get unique desktops by connecting to port 5900.
If the VNC server is exposed to the internet, add the -localhost option to Xvnc in xvnc@.service (note that -query localhost and -localhost are different switches) and follow #Accessing vncserver via SSH tunnels. Since we only select a user after connecting, the VNC server runs as user nobody and uses Xvnc directly instead of the vncserver script, so any options in
/.vnc are ignored. Optionally, autostart vncconfig so that the clipboard works (vncconfig exits immediately in non-VNC sessions). One way is to create:
Connecting to vncserver
Any number of clients can connect to a vncserver. A simple example is given below where vncserver is running on 10.1.10.2 port 5901, or :1 in shorthand notation:
Passwordless authentication
The -passwd switch allows one to define the location of the server’s
/.vnc/passwd file. It is expected that the user has access to this file on the server through SSH or through physical access. In either case, place that file on the client’s file system in a safe location, i.e. one that has read access ONLY to the expected user.
The password can also be provided directly.
Example GUI-based clients
TigerVNC’s vncviewer also has a simple GUI when run without any parameters:
Accessing vncserver via SSH tunnels
For servers offering SSH connection, an advantage of this method is that it is not necessary to open any other port than the already opened SSH port to the outside, since the VNC traffic is tunneled through the SSH port.
On the server
On the server side, vncserver or x0vncserver must be run.
When running either one of these, it is recommended to use the localhost option in
/.vnc/config or the -localhost switch (for x0vncserver) since it allows connections from the localhost only and by analogy, only from users ssh’ed and authenticated on the box. For example:
Make sure to Start or Restart the vncserver@.service , for example (see also #Initial setup):
or for x0vncserver:
On the client
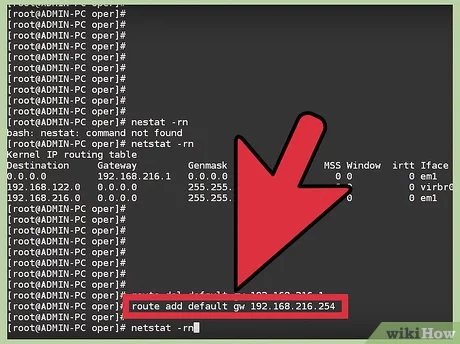
The VNC server has been setup on the remote machine to only accept local connections. Now, the client must open a secure shell with the remote machine (10.1.10.2 in this example) and create a tunnel from the client port, for instance 9901, to the remote server 5901 port. For more details on this feature, see OpenSSH#Forwarding other ports and ssh(1) .
Once connected via SSH, leave this shell window open since it is acting as the secured tunnel with the server. Alternatively, directly run SSH in the background using the -f option. On the client side, to connect via this encrypted tunnel, point the vncviewer to the forwarded client port on the localhost.
What happens in practice is that the vncviewer connects locally to port 9901 which is tunneled to the server’s localhost port 5901. The connection is established to the right port within the secure shell.
What it does is that the -f switch will make ssh go in the background, it will still be alive executing sleep 10 . vncviewer is then executed and ssh remains open in the background as long as vncviewer makes use of the tunnel. ssh will close once the tunnel is dropped which is the wanted behavior.
Alternatively, vncviewer’s -via switch provides a shortcut for the above command:
(Notice the double colon – vncviewer’s syntax is [host]:[display#] or [host]::[port] .)
Connecting to a vncserver from Android devices over SSH
To connect to a VNC server over SSH using an Android device as a client, consider having the following setup:
- SSH running on the server
- vncserver running on server (with -localhost flag for security)
- SSH client on the Android device: ConnectBot is a popular choice and will be used in this guide as an example
- VNC client on the Android device: androidVNC used here
In ConnectBot, connect to the desired machine. Tap the options key, select Port Forwards and add a port:
In androidVNC connect to the VNC port, this is the local address following the SSH connection:
Tips and tricks
Connecting to an OSX system
Recommended security settings
If not #Accessing vncserver via SSH tunnels where the identification and the encryption are handled via SSH, it is recommended to use X509Vnc, as TLSVnc lacks identity verification.
Issuing x509 certificates is beyond the scope of this guide. However, Let’s Encrypt provides an easy way to do so. Alternatively, one can issue certificates using OpenSSL, share the public key with the client and specify it with the -X509CA parameter. An example is given below the server is running on 10.1.10.2:
Toggling fullscreen
This can be done through vnc client’s menu. By default, vnc client’s mkey is F8 .
Workaround for mouse back and forward buttons not working
The VNC protocol currently only uses 7 mouse buttons (left, middle, right, scroll up, scroll down, scroll left, scroll right) which means if your mouse has a back and a forward button these are not usable and input will be ignored.
evrouter can be used to work around this limitation by sending keyboard key presses when clicking the mouse back/forward buttons. Optionally xte found in xautomation and xbindkeys can be used on the server to map the keyboard key presses back to mouse button clicks if needed.
Substituting mouse back/forward buttons with keyboard keys XF86Back/XF86Forward
This method is simple and suitable if you only need a way to navigate backward/forward while using web browsers or file browsers for example.
Install evrouter AUR and xautomation on the client. Configure evrouter, see Mouse buttons#evrouter and evrouter man pages for instructions and tips on how to find the correct device name, window name, button names etc. Example config:
Start evrouter on the client. With above configuration keyboard key XF86Back is sent to the VNC server when clicking the back button on the mouse, and XF86Forward is sent when clicking the forward button.
Mapping the keyboard key presses back to mouse button clicks on the server
If needed it’s possible to map the keyboard keys back to mouse button clicks on the server. In this case it might be a good idea to use keyboard keys which are never on the client or server. In the example below keyboard keys XF86Launch8/XF86Launch9 are used as mouse buttons 8/9.
Evrouter configuration on the client:
Install xautomation and xbindkeys on the server. Configure xbindkeys to map keyboard keys XF86Launch8/XF86Launch9 to mouse buttons 8/9 with xte.
Start xbindkeys $ xbindkeys -f
/.xbindkeysrc . The server will now map XF86Launch8/XF86Launch9 to mouse buttons 8/9.
Troubleshooting
Terminals in vncserver start in / (root dir)
Unable to type ‘
If pressing on a remote client emits the > character, try remapping the incoming key [1] [dead link 2020-04-03 ⓘ] :
Black rectangle instead of window
Most probably this is due to the application strictly requiring the composite Xorg extension. For example webkit based app: midori, psi-plus, etc.
Restart vncserver in this case using something like following:
It looks like Composite extension in VNC will work only with 24bit depth.
Empty black window with mouse cursor
Verify that the user is not logged into a physical X session, unless this option was configured with x0vncserver . Multiple X sessions for a single user are not supported, see https://github.com/TigerVNC/tigervnc/issues/684#issuecomment-494385395.
Conversely, trying to log into a local X session while a VNC server service is running for that user will likely not work, and you may get stuck on a splash screen when using a desktop environment.
No mouse cursor
If no mouse cursor is visible when using x0vncserver, start vncviewer as follows:
Alternatively, put DotWhenNoCursor=1 in the TigerVNC configuration file, which is at
/.vnc/default.tigervnc by default.
Copying clipboard content from the remote machine
If copying from the remote machine to the local machine does not work, run autocutsel on the server, as mentioned in [2]:
Now press F8 to display the VNC menu popup, and select Clipboard: local -> remote option.
«Authentication is required to create a color managed device» dialog when launching GNOME 3
A workaround is to create a «vnc» group and add the gdm user and any other users using vnc to that group. Modify /etc/polkit-1/rules.d/gnome-vnc.rules with the following[3]:
No window decoration / borders / titlebars / cannot move windows around
Start a window manager to fix an empty xterm frame. For example, on Xfce, run xfwm4 & .
systemd service unit run as user
Create the following template:
Start/enable tigervnc@:9 to run the template instance on display 9.
Источник
Arch Linux User Repository
Search Criteria
Package Details: realvnc-vnc-server 6.7.4-1
Package Actions
| Git Clone URL: | https://aur.archlinux.org/realvnc-vnc-server.git (read-only, click to copy) |
|---|---|
| Package Base: | realvnc-vnc-server |
| Description: | VNC remote desktop server software by RealVNC |
| Upstream URL: | https://www.realvnc.com/ |
| Keywords: | connect realvnc vnc |
| Licenses: | custom |
| Conflicts: | tigervnc, tightvnc, turbovnc |
| Submitter: | ava1ar |
| Maintainer: | ava1ar (Kewl) |
| Last Packager: | Kewl |
| Votes: | 10 |
| Popularity: | 0.000193 |
| First Submitted: | 2017-09-11 23:39 |
| Last Updated: | 2021-03-31 13:12 |
Dependencies (4)
Required by (0)
Sources (6)
- https://www.realvnc.com/download/file/vnc.files/VNC-Server-6.7.4-Linux-ARM.deb(armv7h)
- https://www.realvnc.com/download/file/vnc.files/VNC-Server-6.7.4-Linux-ARM.deb(armv7)
- https://www.realvnc.com/download/file/vnc.files/VNC-Server-6.7.4-Linux-ARM.deb(armv8)
- https://www.realvnc.com/download/file/vnc.files/VNC-Server-6.7.4-Linux-ARM.deb(aarch64)
- https://www.realvnc.com/download/file/vnc.files/VNC-Server-6.7.4-Linux-x64.deb(x86_64)
- https://www.realvnc.com/download/file/vnc.files/VNC-Server-6.7.4-Linux-x86.deb(i686)
Latest Comments
BenTheTechGuy commented on 2021-05-04 21:01
Because of this versioning and upstream conflict issue, I made a new package to maintain the aarch64 version exclusively. @Kewl: Please remove armv7 , armv8 , and aarch64 from your architectures.
azasouth commented on 2021-04-21 10:15
@Kewl there is no arm64 version of v6.7.4 as yet. The highest 64bit version is v6.7.2. Official Realvnc only produce a 32bit version currently. Raspberrypi.org have ported a 64bit version themselves thus why the upstream source for the 64bit version is http://archive.raspberrypi.org/debian/pool/main/r/realvnc-vnc/realvnc-vnc-server_6.7.2.43081_arm64.deb
Kewl commented on 2021-04-21 07:10
@AzaSouth where can we find v6.7.4 for aarch64? this package is for the latest version
azasouth commented on 2021-04-21 01:40
I have modified the PKGBUILD to have a working realvnc server aarch64 version that has been tested on a Raspberry Pi4 8Gb with a vanilla ArchLinuxARM64 install: https://github.com/azalinux/realvnc-server-aarch64-archlinuxarm If you would like me to add this package to the AUR separately please let me know 🙂
Kewl commented on 2021-04-15 20:22
I can remove armv7 and armv8 from next release. For other changes, please propose a working PKGBUILD as I cannot test other architectures myself.
MattScherbatsky commented on 2021-04-15 19:17
Thank you @BenTheTechGuy! Modified this PKGBUILD during installation to use http://archive.raspberrypi.org/debian/pool/main/r/realvnc-vnc/realvnc-vnc-server_6.7.2.43081_arm64.deb with ‘7e6d0bea799a71c75c72b82073e5f3e6’ md5sum. And then: sudo cp /opt/vc/lib/libbcm_host.so /usr/lib/libbcm_host.so.0 (same for libvcos.so and libvchiq_arm.so)
This works on Manjaro ARM (RPi 3B+)
BenTheTechGuy commented on 2021-02-18 22:08
Also please remove armv7 and armv8 as they’re not real architectures. The official architectures are: arm (armv5), armv6h, armv7h, and aarch64.
void09 commented on 2021-01-06 22:26
Please do remove aarch64 at least, as the previous user said, tested and it’s not working for me.
Kewl commented on 2019-09-28 07:56
@anch2150 thanks for your input, ARM is not officially supported in Arch and I have no knowledge of it, please confirm which ones to drop/keep/add.
anch2150 commented on 2019-09-28 00:57
Please consider removing aarch64 and armv8 as the official ARM release is armhf only.
Copyright © 2004-2021 aurweb Development Team.
AUR packages are user produced content. Any use of the provided files is at your own risk.
Источник